5 Proven Risk Mitigation Strategies to Protect Your Business in 2026

Businesses that neglect mitigation strategies face financial losses, legal penalties, and long-term reputational damage. Companies that ignore compliance risk fines and regulatory scrutiny. They may even lose their business license. Risk mitigation is the process of identifying, assessing, and prioritizing risks to prepare for reducing the effects a company faces. But the right risk mitigation strategies can save substantial amounts of money and protect brand image. We've outlined five proven mitigation strategies to help you safeguard your business in 2026.
Risk Avoidance: Eliminating Threats Before They Occur

Image Source: Hyperproof
Risk avoidance stands as the most direct approach among mitigation strategies. This risk mitigation strategy involves taking actions you think over carefully to eliminate potential hazards, threats, or exposures that could negatively affect your organization [1]. Risk reduction seeks to minimize probability or impact. Risk avoidance aims to prevent the possibility of harm entirely by steering clear of certain activities or decisions [1].
What is Risk Avoidance
Risk avoidance means identifying potential risks and taking proactive steps to eliminate the possibility of those risks occurring [2]. The strategy focuses on removing any threat, hazard, or risk event that might negatively impact the organization [3]. This is different from ignoring a risk or failing to identify it. Risk avoidance requires careful thinking, risk analysis, planning, and execution [3].
The approach works by deflecting threats and removing the chances that they could result in unexpected or damaging consequences [3]. A building company that halts all construction work during an electrical storm demonstrates clear risk avoidance to avoid injury risks [4]. A utility company running critical systems on an air-gapped network completely isolated from other networks eliminates the risk of cyberattacks [4].
When to Use This Mitigation Strategy
Risk avoidance works best in specific scenarios where the potential negative consequences outweigh the benefits or when risks are deemed unacceptable [1]. This mitigation strategy becomes especially relevant when dealing with high-impact, high-probability risks that could disrupt operations severely, tarnish your brand, or lead to significant financial losses [1].
Legal and regulatory compliance situations call for risk avoidance when a particular activity poses high risk of violating laws, regulations, or ethical standards [1]. Companies may decide not to participate in business practices legal in some jurisdictions but not others to avoid legal penalties [2].
High probability of failure scenarios justify avoidance. Projects, investments, or ventures with low chances of success or economic viability warrant this approach [1]. A tech firm lacking manufacturing experience might avoid developing hardware due to quality control issues and supply chain disruptions [1].
Uncertainty and limited information environments make risk avoidance sensible when risks are difficult to measure or predict accurately [1]. An organization might choose not to pursue a project with uncertain regulatory approval and avoid cancelation or delays [2].
Strategic focus considerations matter. Avoidance makes sense if a potential risk doesn't arrange with long-term strategic goals [1]. A company building a reputation for premium products might avoid entering low-cost markets to maintain brand integrity.
Ethical considerations sometimes demand avoidance. The ethical risks justify avoiding that market altogether when entering a new market would require compromising labor standards or environmental regulations [1].
How to Implement Risk Avoidance
A methodical process guides the implementation of risk avoidance as a mitigation strategy:
- Identify Risks: Analyze the context, understand potential negative consequences, and recognize factors contributing to risks associated with specific activities, decisions, or situations [1].
- Evaluate Risk Severity: Determine the potential impact or harm a risk could cause and evaluate the likelihood of occurrence to prioritize which risks need immediate attention and avoidance measures [1].
- Assess Avoidability: Think over whether feasible alternative strategies, processes, or decisions exist that would eliminate or reduce exposure to the risks significantly [1].
- Develop Risk Avoidance Strategies: Create strategies that may involve alternative approaches, revised processes, or refraining from certain activities or decisions altogether [1].
- Implement Preventive Measures: Execute the plan by revising plans, modifying processes, or establishing guidelines and protocols to ensure risks are avoided effectively [1].
- Monitor and Review: Review and assess progress regularly to ensure intended risk avoidance measures are being followed and address any potential new risks promptly [1].
- Adjust as Necessary: Make adjustments or improvements to strategies when new risks emerge or effectiveness proves unsatisfactory by updating protocols, enhancing training, or revising processes [1].
- Communicate and Educate: Ensure all relevant stakeholders understand the risks, the risk avoidance strategies in place, and their roles and responsibilities in implementing them [1].
Ground Examples
Construction: Falls from heights represent significant risks leading to severe injuries or fatalities. Risk avoidance measures include using scaffolding systems to provide stable platforms, installing guardrails and toeboards on elevated work platforms, and changing project scope altogether to eliminate working at heights when possible [1].
Manufacturing: Mishandling hazardous materials poses risks including chemical spills, fires, explosions, and health hazards. Companies avoid these risks by substituting hazardous materials with less hazardous alternatives, training employees on proper handling techniques and PPE use, and installing adequate ventilation systems to control harmful substance concentrations [1].
Retail: Unauthorized access to customer payment information and data breaches can cause financial losses and reputational damage. Retailers implement secure payment processing systems complying with PCI DSS standards, grant data access privileges based on least privilege principles, and decide not to collect certain data types lacking known protection measures [1].
Project Management: Procurement risks include delays, cost overruns, quality issues, and supplier failures. Organizations avoid partnering with vendors having poor performance histories, prequalify suppliers based on experience and financial stability, and vary supplier bases to prevent disruptions [1].
Cybersecurity: Unauthorized access to critical systems can lead to data breaches and intellectual property loss. Companies create network barriers through firewalls preventing unauthorized lateral movement, implement Two-Factor or Multi-Factor Authentication, and apply strong encryption protocols for sensitive data [1].
Risk Transference: Sharing the Burden with Third Parties

Image Source: Hyperproof
Transferring financial responsibility to external parties represents a strategic reduction strategy when risks cannot be eliminated but need protection mechanisms. Risk transference shifts potential financial liability from your organization to another entity through insurance contracts, legal agreements, or financial instruments [2]. This approach is different from risk avoidance because the risk continues to exist, only the responsibility for it moves from your organization to another party [5].
What is Risk Transference
Risk transference involves one party assuming the liabilities of another party through contractual arrangements [2]. The fundamental mechanism operates by shifting financial responsibility and what it all means for specific risks to third parties better positioned to manage them [6]. Unlike risk acceptance where you knowingly bear consequences, transference proactively allocates the burden to entities with appropriate resources and capabilities [6].
You provide periodic payments such as insurance premiums to compensate the third party for bearing the risk [2]. This creates a defined exchange of value where the transferring party gains financial protection while the accepting party receives compensation for assuming potential losses. The process works through legally binding agreements that clearly assign responsibility for certain risks to another party [6].
An important difference exists, though: you can outsource the process, but you cannot fully outsource the risk itself [5]. Although liability and financial effect may transfer, reputational consequences and operational effects often remain with your organization [5]. Automakers outsourced airbag manufacturing to Takata, and the manufacturer bore responsibility for defects, yet Ford, Toyota, and others still faced reputational fallout and stock price effects [5].
When to Use This Mitigation Strategy
Risk transference proves valuable for risks with low probability of occurring but high potential effect [6]. Transferring that burden makes strategic sense when financial consequences of an event could destabilize your organization. This reduction strategy applies especially to risks that are difficult or costly to manage internally [6].
Organizations should think about transference when specialized expertise exists elsewhere. Hiring a specialized IT security firm to manage cybersecurity risks exemplifies this approach [2]. Outsourcing manufacturing to companies with expertise in handling production-related risks transfers associated operational hazards [2].
Financial stability concerns justify transference. You protect against large financial losses that could threaten business continuity by limiting liability associated with specific risks [2]. Monthly premiums provide more predictable costs than unexpected catastrophic losses and make budgeting and financial planning more manageable.
Regulatory requirements in certain industries mandate maintaining specific insurance or financial protections [2]. Risk transference mechanisms provide documentation of compliance while protecting your organization from covered events at the same time.
How to Implement Risk Transference
You need methodical planning and execution to implement risk transference. Identify and measure risks first to understand what needs protection and potential effect [2]. This foundational step ensures awareness of risks and their consequences before attempting transfer.
Think about the cost-benefit ratio by weighing insurance premiums or higher contract prices against potential loss probability and magnitude [2]. While transference requires ongoing payments, compare these costs to the financial devastation of experiencing the risk event without protection.
Verify contract precision through careful review of all agreements and policies [2]. Fine print matters, especially exclusions and limitations in coverage. Understanding what situations remain uncovered prevents false security assumptions. Insurance policies include conditions that must be met before payouts occur, along with situations not covered depending on cause [6].
Choose partners with financial stability since their ability to fulfill obligations proves vital for effective risk transfer [2]. Whether selecting an insurance carrier, contractor, or service provider, verify their financial strength and track record of honoring commitments.
Regularly review risk transfers as your business evolves and the risk landscape changes [2]. Update arrangements to reflect current operations, emerging threats, and modified business activities. Request certificates of insurance from third parties to verify adequate coverage exists [6]. Review these certificates regularly to ensure coverage remains sufficient and current for ongoing relationships.
Request additional insured status on third-party insurance policies whenever possible for extra protection [6]. This ensures coverage under their policy provides direct protection for your organization.
Ground Examples
Insurance policies provide the most common transference method. Organizations pay premiums to insurance companies for financial protection against losses [2]. Property insurance protects against physical damage, general liability insurance covers third-party injury claims, and professional liability addresses errors in services provided. Cyber insurance has grown by a lot and covers costs related to data recovery, legal fees, and public relations efforts after breaches [6].
Contractual clauses shift risks through legal provisions. Indemnification clauses ensure potential losses will be compensated by the opposing party [2]. Contractors assume risks associated with project delays or damages through specific agreement terms in construction contracts [6]. Hold harmless agreements and limitation of liability clauses commonly appear in vendor and supplier contracts [2].
Outsourcing functions transfers operational risks to external service providers. Companies outsource customer service, order fulfillment, or payroll services to focus on core competencies while transferring associated risks [6]. Organizations may select providers in different geographical regions to reduce location-specific risks like weather events [6]. Software-as-a-Service (SaaS) moves technical risk and recovery risk to the provider along with business risk it reduces [6].
Subcontracting moves specified project risks to specialized contractors. General contractors transfer electrical work risks to electricians who assume responsibility for proper installation and code compliance in construction projects [2]. This approach utilizes specialized expertise while protecting the primary contractor from technical failures.
Hedging strategies use financial instruments like derivatives to transfer market-related risks [5]. Organizations protect against adverse price movements, currency fluctuations, or interest rate changes by entering hedge contracts [6]. This proves valuable in finance and commodities industries where market volatility creates significant exposure.
Risk Reduction: Minimizing Impact Through Controls
Image Source: Ncontracts
Implementing controls to manage existing risks represents a practical reduction strategy when elimination or transfer proves impossible or impractical. Risk reduction deals with reducing potential losses through a staggered approach rather than attempting complete elimination [6]. This strategy acknowledges that certain hazards will remain part of operations, yet their severity and likelihood can be decreased through systematic controls and measures.
What is Risk Reduction
Risk reduction refers to processes, controls and measures designed to reduce the risk organizations face on a regular basis [6]. The approach involves identifying and assessing risks while implementing various measures to reduce them [6]. Organizations perform risk reduction to minimize harm and adverse effects from these risks [6].
The fundamental principle recognizes you cannot eliminate all risks, no matter how careful operations are [6]. The best approach involves minimizing and reducing certain risks through controls. Risk reduction modifies operational risks and financial policies to reduce their potential negative effects on the business [7]. Control measures modify these risks by implementing safeguards and procedures intended to prevent, detect and respond to them [7].
Financial variation stands as one of the most reliable risk reduction strategies [6]. When your financial risk is varied, adverse side effects are diluted [6]. An investor owning oil stocks can reduce risk by varying their portfolio, keeping oil stocks while buying stocks in other industries that tend to move in opposite directions to oil equities [6]. If you have several income streams, losing one stream won't hurt as much if only 25% of income comes from that stream [6].
When to Use This Reduction Strategy
Risk reduction becomes the appropriate strategy when risks cannot be avoided but their effect requires management. This approach applies to inherent risks that form part of operating a business [6]. Whatever your industry, target market and personnel, you will always face certain risk levels while operating [6].
Organizations should employ risk reduction when the chance of risks causing financial or adverse harm exists without measures in place [6]. The strategy proves valuable for risks that can be reduced through safety equipment or behavioral changes [6]. Risk reduction requires constant monitoring and attention, unlike accepting, transferring or avoiding identified risks which require minimal effort from managers or employees [6].
How to Implement Risk Reduction
Successful implementation begins with identifying and assessing risks your company faces throughout operations [6]. Conduct risk audits and inspections to determine your risks, then assess and rank them based on severity or urgency [6].
Organizations must think over all possible control measures and determine which are most effective and practical for each risk [8]. Risk managers should develop a proactive approach by selecting controls that reduce risk before it occurs rather than implementing corrective measures after a key risk indicator has already reached a high level [8].
Many firms use preventive controls like strict policies, processes, procedure documents or safety and security equipment such as antivirus or firewalls that lower risk [8]. Some risk types require detective controls like audits, inspections, checks, monitoring, surveillance and incident reporting [8]. Corrective controls involve measures like patch updates, root cause analysis and training to lower risk levels that are too high [8]. Reducing controls transfer risk through purchasing insurance, implementing contingencies and backups, and formulating business continuity plans to defer operational risk [8].
Control testing proves key to meet compliance requirements and ensure controls function as intended to protect the organization [8]. Testing methods could include questionnaires, observations, inspections and review of relevant documents and records to verify effectiveness [8]. If controls are not functioning or found ineffective, new or improved controls must be put in place to reduce the impending risk [8].
Teams can identify common factors contributing to failure or inefficiency of a risk control by exploring past incidents and operational data [8]. If data reveals equipment failures occur more frequently after certain usage thresholds, you can schedule maintenance controls before reaching those points to reduce risk [8].
Real-Life Examples
British Petroleum implemented several risk control measures following the Deepwater Horizon oil spill in 2010 [5]. BP focused on improving its safety culture, including conducting safety training and drills for employees, investing in advanced technology for better monitoring and control of drilling operations, and implementing rigorous safety standards across its global operations [5].
Starbucks adopted a varied sourcing strategy to address supply chain risks [5]. The company sources coffee beans from multiple regions worldwide, making it vulnerable to fluctuations in supply and potential disruptions due to weather, political instability or other unforeseen events [5]. Procuring coffee beans from a wide range of suppliers across different regions helps reduce reliance on any single supplier or region, ensuring steady supply and minimizing the effect of potential disruptions [5].
A food processing company identified contamination as a critical issue [9]. The company implemented rigorous supplier audit programs with on-site visits, introduced multi-layered testing protocols for raw materials and finished products, conducted training sessions for employees on hygiene practices, and invested in robust traceability systems allowing real-time tracking of products from raw material procurement to finished product distribution [9].
Risk Acceptance: Strategic Decision-Making for Low-Priority Threats

Image Source: Hyperproof
Sometimes the most strategic mitigation strategy involves acknowledging a risk exists and choosing not to act on it right away. Risk acceptance occurs when a business or individual acknowledges that the potential loss from a risk is not great enough to warrant spending money to avoid it [10]. This approach represents a conscious decision to live with a risk rather than taking steps to eliminate or reduce it. We also know it as risk retention [11].
What is Risk Acceptance
Risk acceptance means recognizing a risk and deciding that the potential downside is manageable or that the cost of mitigation exceeds the potential effect of the risk itself [12]. This mitigation strategy is different from ignoring a risk. Accepting risk constitutes a calculated choice to let certain vulnerabilities exist while directing efforts toward more pressing threats [11].
Organizations employ risk acceptance when other response options are unavailable or not optimal [2]. Risk acceptance is a status quo response where risk owners acknowledge the risk exists but accept it with minimal action [2]. An acceptance strategy may be appropriate if the cost of other responses exceeds the value that would be gained [2].
Risk acceptance takes two simple forms. Passive acceptance indicates an organization is aware of a risk but has no mitigation plan to respond to that risk [13]. An organization understands that some employees leave the company with no notice, but it doesn't have a human resources strategy in place to replace them [13]. Active acceptance means the organization is aware of a risk and has a recognized contingency plan for incident response if that risk rises above a threshold requiring mitigation [13]. An organization acknowledges supply chain vulnerabilities and develops a response playbook in case the risk materializes [13].
When to Use This Mitigation Strategy
This mitigation strategy applies to infrequent and small risks that do not have the potential to be catastrophic or otherwise too expensive [10]. Risk acceptance becomes viable when the likelihood of occurrence or potential effect is low, when mitigation measures are impractical, or when the cost of mitigation exceeds the asset's value at risk [14].
Several conditions support risk acceptance decisions. Low probability situations occur when the risk is unlikely to occur at all [13]. Marginal effect applies when the business effect is low, such as occasional minor equipment failures [13]. High mitigation cost justifies acceptance when the cost of mitigation outstrips potential financial losses from the risk [13]. Organizations with a healthy risk appetite accept risks within their tolerance levels [13]. Any accepted risk must adhere to regulatory compliance requirements [13].
How to Implement Risk Acceptance
Structured documentation and oversight are required to implement risk acceptance. Organizations cannot accept a risk without first scrutinizing and understanding its severity [13]. Teams document the risks, assign ownership, and track them over time. This frees up capacity for more urgent matters while ensuring nothing falls through the cracks [11].
Every accepted risk needs a clear owner responsible for monitoring it and reassessing it when necessary [11]. Documentation should outline why the decision to accept the risk makes sense in the current context. Data such as incident reports, financial estimates, and industry standards support the case [11]. Organizations should set timelines for reassessment, which are quarterly or semi-annual depending on the risk's nature. This includes specific triggers that would warrant an earlier review [11].
Senior leadership or the risk committee should sign off on accepted risks to ensure alignment across the organization [11]. This acknowledges that the risk exists and has been consciously accepted at the right level of authority [11]. Risk acceptance may appear to be a passive response, but organizations should take a more active approach when risk acceptance relates to higher assessed risk [2].
Ground Examples
A company continues to operate legacy software that no longer receives security updates [11]. Upgrading the system would cost AUD 764,495.12 and require six months of downtime, while the estimated financial effect of a potential breach is AUD 76,449.51 [11]. The company decides to accept the risk, documenting the decision through a risk acceptance form, assigning ownership to the IT team, and implementing compensating controls [11].
An IT department became aware of the risk acceptance approach to action plans and latched onto it with great enthusiasm, using it more than comfortable [2]. The audit manager sensed an abuse of the system and crafted a process where key stakeholders were informed of and agreed with the decision [2]. The document would be sent to the business unit leader for approval and signature for moderate assessed risks, while for high assessed risks, the document was sent to the CEO for approval and signature [2]. This process changed IT management's position on the use of risk acceptance responses, and the frequency of risk acceptance dropped considerably [2].
Risk Monitoring: Continuous Oversight and Response
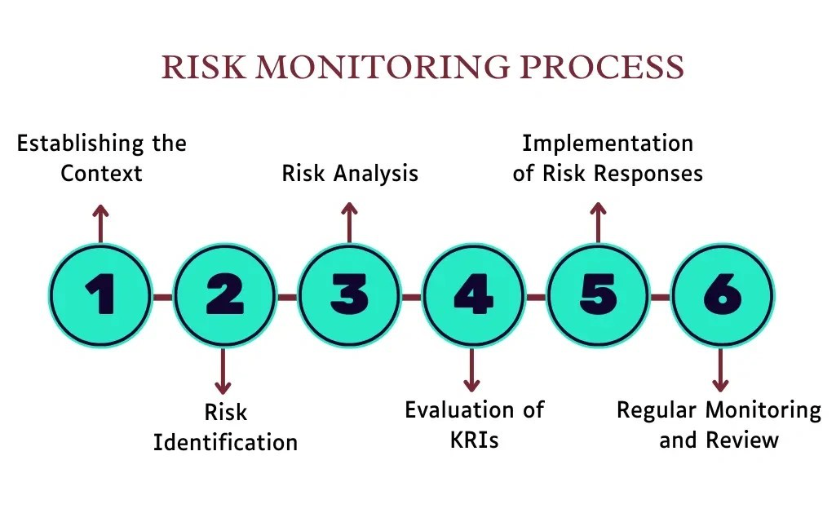
Image Source: Metricstream
Ongoing alertness over your risk landscape represents the foundation of a resilient mitigation strategy. Risk monitoring is the continuous process of identifying, analyzing, and managing risk throughout a business's lifecycle [6]. Previous mitigation strategies address specific risks at particular points. Monitoring provides perpetual oversight of your organization's entire risk environment.
What is Risk Monitoring
Risk monitoring involves tracking identified risks, detecting new ones, and evaluating risk response effectiveness throughout operations [15]. The process delivers ongoing insight into exposures that could affect objectives rather than providing snapshots at given points in time [16]. Key components include continuous assessment, key risk indicators, collaboration across departments, and adaptation to changing circumstances [6].
This mitigation strategy will give a recognized risk environment, identifies and includes new risks in planning, keeps identified risks within acceptable limits, and deals with risk events [17]. The approach requires reviewing and monitoring the risk landscape to capture any changes in the external environment or within the organization itself that may affect risk exposure [6].
When to Use This Mitigation Strategy
Risk monitoring applies as an essential ongoing practice rather than a situational response. Organizations should employ continuous monitoring when regulatory, cybersecurity, and strategic risks move faster than static assessments can track [18]. This mitigation strategy proves valuable for high-velocity risks like data breaches or regulatory changes that offer little warning and need quicker action [18].
Monitoring becomes necessary when compliance obligations must be met to reduce the likelihood of breaches, fines, or reputational damage [16]. Organizations apply continuous monitoring across compliance, operational, financial, and strategic risks [16].
How to Implement Risk Monitoring
Implementation begins with establishing a detailed framework that outlines processes, methodologies, and tools for identifying, assessing, monitoring, and mitigating risks aligned with organizational objectives [6]. Assign clear ownership and accountability for monitoring specific risks at different organizational levels [6].
Identify and monitor key risk indicators that signal increases in risk levels, ranging from financial ratios and operational metrics to compliance indicators providing early warnings [6]. Modern organizations use technology through risk management software that streamlines monitoring with up-to-the-minute data analysis, dashboards for visualization, and alerts for immediate attention [6].
Ground Examples
A global manufacturer with complex supply chains uses continuous monitoring tools to detect disruptions such as vendor shutdowns or shipping delays before they cascade into operational bottlenecks [16]. Banks employ ongoing credit risk monitoring where regulators gain confidence through evidence of timely detection and remediation [16].
Comparison Table
Comparison Table: 5 Proven Risk Mitigation Strategies
Strategy
Definition
Primary Purpose
When to Use
Key Implementation Steps
Ground Examples
Risk Avoidance
Taking considered actions to eliminate potential hazards, threats, or exposures that could negatively affect your organization
Prevent the possibility of harm entirely by steering clear of certain activities or decisions
High-impact, high-probability risks; legal/regulatory compliance issues; high probability of failure scenarios; uncertainty and limited information environments
1. Identify risks2. Review risk severity3. Assess avoidability4. Develop avoidance strategies5. Implement preventive measures6. Monitor and review7. Adjust as necessary8. Communicate and educate
Construction (fall prevention with support), Manufacturing (hazardous material substitution), Retail (secure payment systems), Project Management (vendor prequalification), Cybersecurity (air-gapped networks)
Risk Transference
Shifting potential financial liability from your organization to another entity through insurance contracts, legal agreements, or financial instruments
Transfer financial responsibility and consequences of specific risks to third parties better positioned to manage them
Low probability but high potential effect risks; risks requiring specialized expertise; financial stability concerns; regulatory compliance requirements
1. Identify and measure risks2. Think over cost-benefit ratio3. Verify contract precision4. Choose financially stable partners5. Review risk transfers regularly6. Request certificates of insurance7. Request additional insured status
Insurance policies (property, liability, cyber), Contractual clauses (indemnification), Outsourcing functions (customer service, payroll), Subcontracting (specialized work), Hedging strategies (financial derivatives)
Risk Reduction
Processes, controls, and measures designed to reduce risks organizations face through a staggered approach
Minimize and reduce certain risks through controls, acknowledging that certain hazards will remain but their severity and likelihood can be decreased
Risks cannot be avoided but their effect requires management; inherent operational risks; risks that can be reduced through safety equipment or behavioral changes
1. Identify and assess risks2. Conduct risk audits and inspections3. Think over all possible control measures4. Implement preventive, detective, and corrective controls5. Test controls regularly6. Get into past incidents and operational data
British Petroleum (post-Deepwater Horizon safety improvements), Starbucks (diversified coffee sourcing), Food processing company (contamination prevention protocols)
Risk Acceptance
Acknowledging that the potential loss from a risk is not great enough to warrant spending money to avoid it; conscious decision to live with a risk
Recognize a risk and decide that the potential downside is manageable or that the cost of mitigation exceeds the potential effect
Infrequent and small risks; low probability situations; marginal effect scenarios; high mitigation cost relative to potential loss; risks within organizational tolerance levels
1. Inspect and understand risk severity2. Document the risks3. Assign clear ownership4. Set timelines for reassessment5. Get senior leadership sign-off6. Track risks over time7. Establish triggers for earlier review
Legacy software operation (cost of upgrade vs. breach effect), IT department risk acceptance process with stakeholder approval requirements
Risk Monitoring
Continuous process of identifying, analyzing, and managing risk throughout a business's lifecycle
Provide perpetual oversight of the organization's entire risk environment with ongoing insight into exposures
Universal ongoing practice; high-velocity risks (data breaches, regulatory changes); compliance obligations; across compliance, operational, and financial risks
1. Establish detailed framework2. Assign clear ownership and accountability3. Identify and monitor key risk indicators4. Utilize technology and risk management software5. Conduct reviews regularly6. Ensure continuous assessment and adaptation
Global manufacturer (supply chain disruption monitoring), Banks (ongoing credit risk monitoring for regulatory compliance)
Conclusion
Implementing these five mitigation strategies might seem overwhelming at first, but you don't need to tackle everything at once. Start by identifying your most critical risks and then determine which strategy fits best. Maybe you'll avoid high-impact threats and transfer financial exposure through insurance. Acceptance makes sense for low-priority concerns. Continuous monitoring will give your efforts the staying power they need.
The important thing is taking action. Pick one strategy that addresses your biggest vulnerability and build from there. Your business deserves protection, and these proven approaches give you a framework to safeguard your operations in 2026 and beyond.
References
[1] - https://safetyculture.com/topics/risk-management/risk-avoidance
[2] - https://internalauditor.theiia.org/en/articles/2022/february/risk-acceptance/
[3] - https://www.zengrc.com/blog/common-risk-management-strategies-risk-avoidance-vs-risk-mitigation/
[4] - https://www.techtarget.com/searchsecurity/definition/risk-avoidance
[5] - https://www.investopedia.com/terms/r/risk-control.asp
[6] - https://www.metricstream.com/learn/risk-monitoring.html
[7] - https://www.dataguard.com/blog/what-are-controls-in-risk-management/?hs_amp=true
[8] - https://riskonnect.com/internal-audit/why-effective-controls-are-essential-to-mitigate-risk/
[9] - https://www.metricstream.com/learn/risk-reduction.html
[10] - https://www.investopedia.com/terms/a/accepting-risk.asp
[11] - https://sprinto.com/blog/risk-acceptance/
[12] - https://www.metricstream.com/learn/risk-acceptance.html
[13] - https://www.techtarget.com/searchcio/definition/risk-acceptance
[14] - https://www.isms.online/glossary/risk-acceptance/
[15] - https://www.theknowledgeacademy.com/blog/risk-monitoring/
[17] - https://www.techtarget.com/searchcio/tip/What-is-risk-monitoring-Definition-and-best-practices
More insights
Ready to Save Lives at Work?
With Impress Solutions, you’re not just getting a service, you’re securing peace of mind with a partner you can trust. Book a free consultation today, and let’s map out how we can help you save lives at work.













.png)











.png)
.png)
.png)
.png)
.png)
.png)
.png)

.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)
.png)



.png)






























.webp)
.webp)

